Les patients sont notre priorité.
Une prise en charge efficace des patients commence par des résultats de tests plus rapides.
Cepheid is dedicated to improving patient outcomes worldwide with fast, accurate tests for diseases like tuberculosis, HCV, and respiratory illnesses.
Sélectionnez votre domaine d’expertise

Santé publique mondiale
Le Programme d’accès mondial (Global Access Program) de Cepheid repose sur la conviction que tout le monde, partout, devrait avoir accès à des tests de diagnostic de haute qualité.
De meilleures réponses conduisent à de meilleurs résultats.
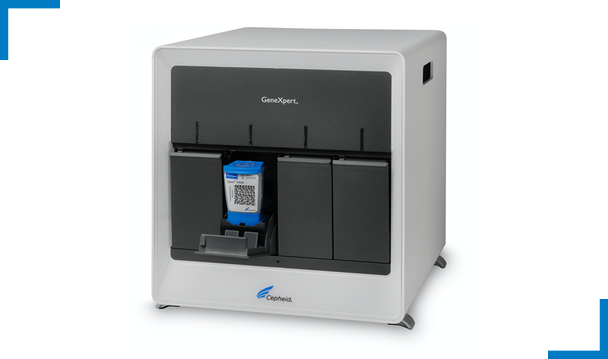
Un système. De multiples tests.
Cepheid's GeneXpert® System is a flexible, fully scalable platform that provides healthcare professionals with a broad test menu for any setting — from the core lab to near patient applications. Découvrez pourquoi les solutions de Cepheid constituent le meilleur choix pour des tests diagnostiques rapides, précis et simples.
Nos formations, ressources et outils peuvent vous ouvrir la voie vers une réussite constante, où que
vous alliez.

Cepheid and Oxford Nanopore Technologies Partner to Advance Automated Sequencing-Based Solutions
Cepheid and Oxford Nanopore Technologies Partner to Advance Automated Sequencing-Based Solutions
Le Dr David H. Persing remporte le prix California Life Sciences Pantheon Award 2024